VMware Datastore Encryption for ISO 27001 is often misunderstood as a single checkbox that solves the whole control problem. The short answer is this: in the March 27, 2026 context, the right ISO 27001 approach is to first separate which workloads live on which datastore type, then apply cluster-level data-at-rest encryption for vSAN where appropriate, and use VM Encryption plus, when needed, storage-array encryption controls for VMFS or NFS based designs. This guide is written for teams that need a design that is technically sound and defensible during audit review.
This guide is especially for:
- VMware and vSphere administrators
- security and compliance teams
- IT leaders preparing for ISO 27001 audits
- storage and virtualization architects
Quick Summary
- ISO/IEC 27001 does not require one VMware checkbox; it requires a risk-based ISMS and protection of confidentiality, integrity, and availability.
- “Datastore encryption” does not mean the same thing across every VMware storage model.
- vSAN officially provides Data-at-Rest Encryption at the cluster level.
- In general vSphere environments, encryption workflows often rely on key provider + VM Encryption policy rather than a universal datastore-wide toggle.
- Encryption work should not start until a key provider is configured and backed up.
- A wrong TPM-only constraint can break cryptographic operations on some hosts.
- The real ISO 27001 value comes from key management, separation of duties, logging, recovery testing, and evidence design working together.
Table of Contents
- What Does VMware Datastore Encryption Mean in ISO 27001 Terms?
- Does the Same Encryption Model Apply to Every Datastore?
- What Are the Technical Prerequisites?
- How Should the ISO 27001 Evidence Set Be Designed?
- What Mistakes Are Most Common?
- Practical Implementation Checklist
- Frequently Asked Questions
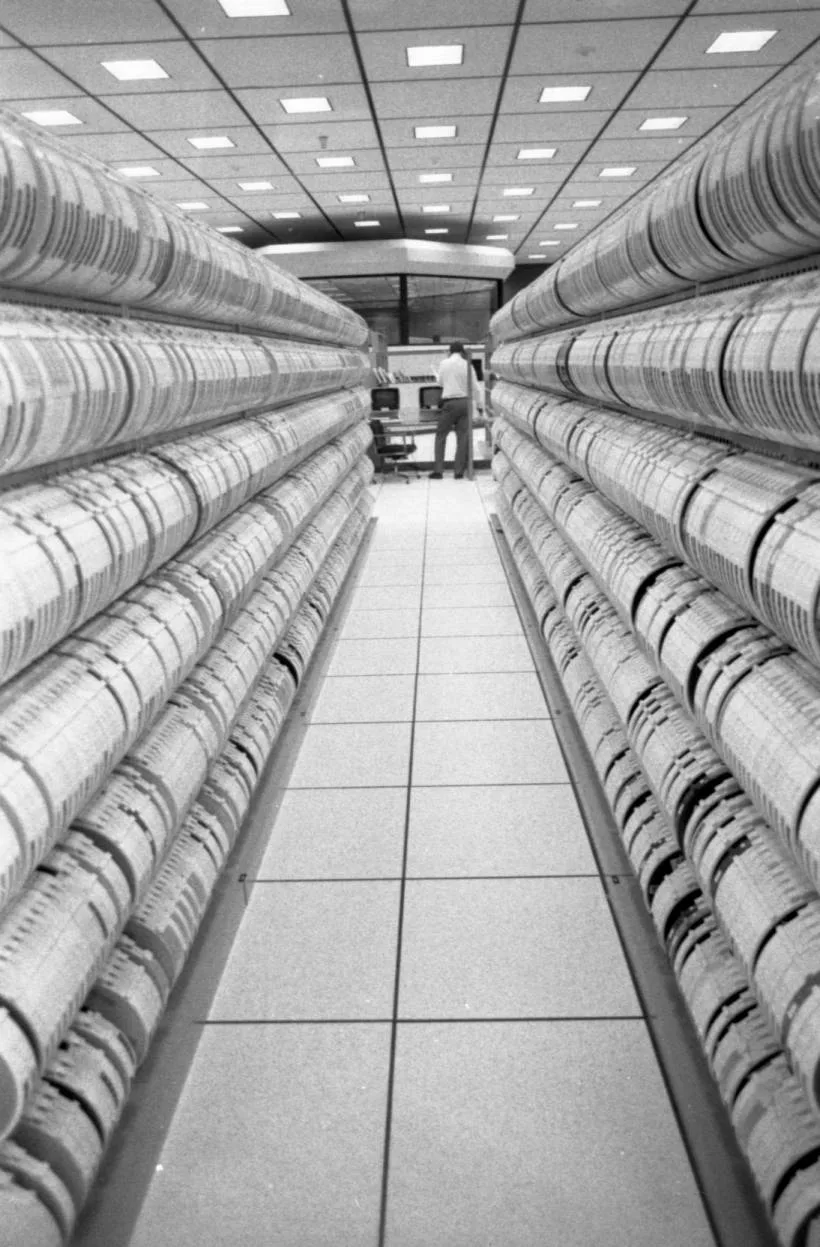
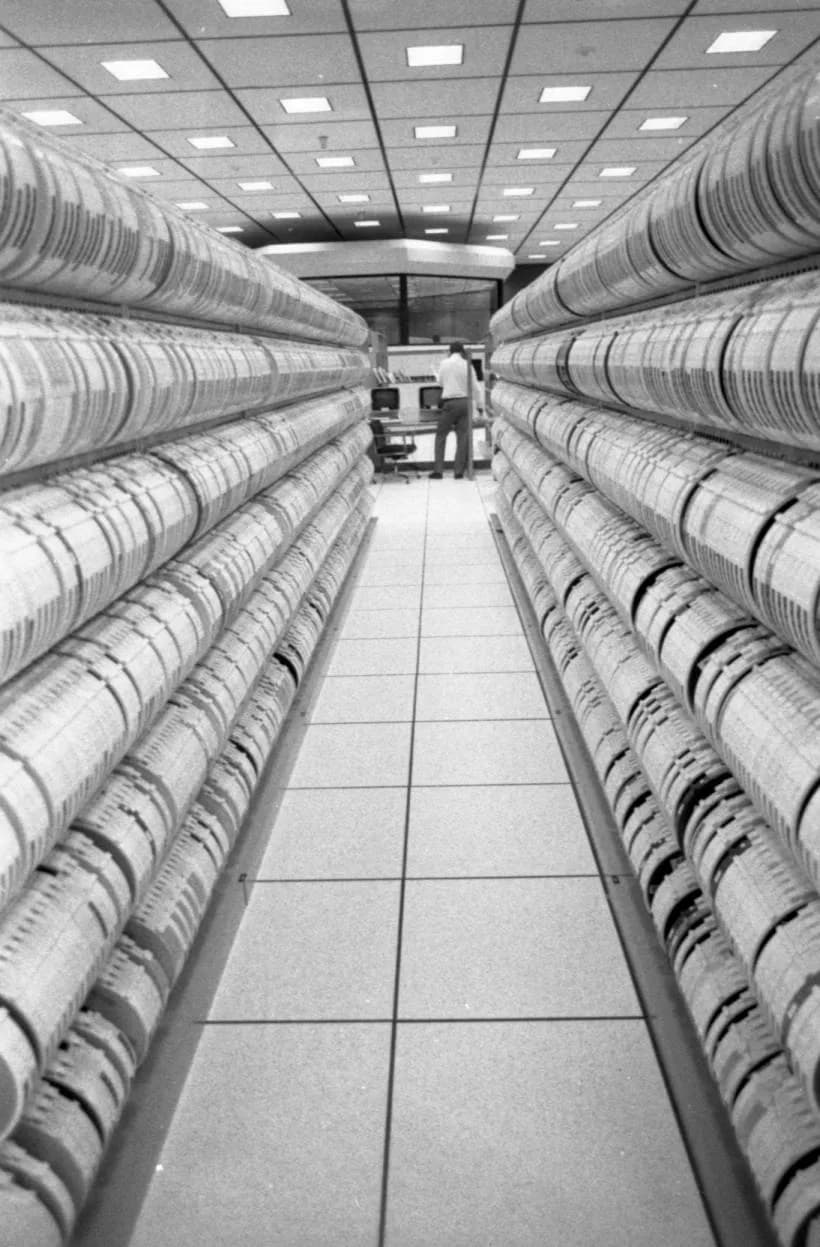
Image: Wikimedia Commons - Inside Data Center.
What Does VMware Datastore Encryption Mean in ISO 27001 Terms?
ISO/IEC 27001 is not about turning on encryption for its own sake. The official ISO explanation says the standard defines requirements for an information security management system and is built around a risk-based approach to protecting confidentiality, integrity, and availability. That means a VMware datastore encryption design is not only a technical choice. It is also a governance and evidence decision.
Before choosing a control, teams should answer:
- what type of data is stored on which datastore
- which workloads require stronger protection because of regulation or contract
- whether the main threat is storage theft, host compromise, administrator misuse, or weak recovery design
- who owns key-management responsibilities
- how logs, alarms, backups, and recovery evidence will be produced
Without these answers, teams usually end up discussing product settings without building a real ISO 27001 control story.
Does the Same Encryption Model Apply to Every Datastore?
No. This is the most important distinction in the whole topic.
If you use vSAN
Broadcom's vSAN Technology Overview states that vSAN provides Data-at-Rest Encryption as a cluster-level feature. The same document explains that this encryption works through VMware vSphere cryptographic modules, does not require self-encrypting drives, and is compatible with KMIP-compliant KMS products as well as VMware's Native Key Provider.
This model is strong when:
- you want one consistent encryption posture for all data stored in the vSAN cluster
- you prefer a cluster-wide storage control
- you want centralized key rotation behavior
If you use VMFS or NFS style datastores
Here, teams should not assume that every datastore has the same “encrypt the datastore” toggle. Broadcom guidance around vTPM and VM encryption shows that the operational workflow often depends on Encrypt VM, the correct key provider, and the appropriate VM storage policy. In other words, for VMFS or NFS based environments the protection model is often focused on encrypting the VM and its files on the datastore, not necessarily flipping one datastore-wide setting.
That leads to a safe implementation inference:
- in vSAN, cluster-level datastore encryption is a primary design pattern
- in VMFS or NFS environments, VM Encryption and storage-array encryption should be evaluated together
If teams skip this distinction, they usually start with the wrong architecture.
What Are the Technical Prerequisites?
1. Do not start without an active key provider
Broadcom KB 396471 is explicit: before you can start encryption tasks, you must configure a vSphere Native Key Provider on vCenter Server. The same article also says that the provider must be backed up before it can be used.
The minimum safe sequence is:
- Create the key provider in vCenter.
- Back up the provider.
- Confirm host access to the provider.
- Apply the correct encryption workflow on the right workload set.
2. Do not leave the TPM-only constraint unchecked or checked by habit
Several Broadcom articles explain that the Use key provider only with TPM protected ESXi hosts option can cause problems in clusters that are not fully TPM-ready. Their official explanation is simple: if TPM protection is enforced, hosts without TPM will not participate in Native Key Provider operations, and cryptographic tasks can fail on those hosts.
This matters especially in:
- mixed or transitional clusters
- older host generations still in service
- environments where TPM exists physically but is not enabled correctly
3. Validate the vCenter 8 encryption flow
Broadcom KB 387992 shows that in vCenter Server 8, when encryption is enabled through the switch, the correct key provider and VM storage policy should be verified. This reduces operational friction, but it should still be documented rather than assumed.
4. Treat backup and recovery as part of encryption design
The key provider backup file is part of the recovery design. Enabling production encryption without a defensible provider backup and recovery process creates a weak availability position under ISO 27001.
Related content:
How Should the ISO 27001 Evidence Set Be Designed?
The most common audit mistake is relying only on screenshots. A much stronger evidence set includes:
- a risk record showing why the workload or datastore required encryption
- the key-provider design and responsibility model
- proof that the key provider backup exists
- configuration records showing where encryption is enabled
- log review and alert monitoring outputs
- restore or recovery test evidence
- change approvals and role-separation records
In this model, datastore encryption is not just a security feature. It becomes a reviewable operational process.
How do technical controls map into audit language?
A practical mapping looks like this:
- Confidentiality: datastore or VM encryption and restricted key access
- Integrity: controlled changes, authorized key-provider operations, and trustworthy logging
- Availability: provider backup, recovery procedure, and tested restoration flow
That is much more convincing than simply saying “encryption is enabled.”
What Mistakes Are Most Common?
Assuming vSAN behavior applies to every datastore
Teams often copy the vSAN cluster-toggle mental model into VMFS or NFS environments. That leads to architecture mistakes very early.
Enabling encryption before backing up the key provider
Broadcom guidance treats provider backup as an essential readiness step. Skipping it weakens the recovery story immediately.
Leaving the TPM option as “recommended” without checking the real cluster
“Recommended” is not the same thing as “correct for every environment.” In mixed clusters it can easily cause production issues.
Treating audit evidence as screenshots only
An ISO 27001 review is much stronger when the technical screen is supported by risk records and operating evidence.
Separating encryption from backup, replication, and DR design
If encrypted workloads are not tested together with backup and recovery procedures, the availability side of the control remains incomplete.
Practical Implementation Checklist
- Datastore types were classified separately.
- The difference between vSAN encryption and VMFS/NFS protection model was documented.
- A Native Key Provider or external KMS design was selected.
- The key provider backup was securely exported and stored.
- The TPM constraint was validated against the real host inventory.
- VM encryption or cluster encryption was verified in a test scope.
- Logs, alerts, and recovery evidence were prepared.
- ISO 27001 risk and process records were updated.
Next Step with LeonX
VMware datastore encryption is not only a settings task. It combines storage architecture, key management, compliance, and recovery discipline. LeonX helps teams deliver the VMware implementation and the ISO 27001 evidence model together instead of treating them as separate projects.
Related pages:
- Business Management Services
- Cybersecurity Assessment Service
- Hardware and Software Solutions
- VMware / Hyper-V / Proxmox Deployment Service
- Contact
Frequently Asked Questions
Is VMware datastore encryption the same feature everywhere?
No. vSAN offers cluster-level data-at-rest encryption, while VMFS and NFS environments often rely on VM Encryption and, when needed, storage-array encryption.
Is Native Key Provider mandatory?
Broadcom documentation is clear that an active key provider is required before encryption tasks can begin. Native Key Provider is the official built-in option when an external KMS is not desired.
Can encryption work on hosts without TPM?
It can, depending on how the environment is designed. The common failure is not always the lack of TPM itself, but enforcing the TPM-only key-provider constraint in the wrong cluster design.
Does ISO 27001 directly require datastore encryption?
No. ISO 27001 does not force one vendor feature. It requires appropriate, risk-based controls for confidentiality, integrity, and availability.
What evidence matters most in audit?
Risk records, key-provider design, backup proof, encryption configuration records, log review, and tested recovery outputs together create the strongest evidence set.
Conclusion
VMware Datastore Encryption for ISO 27001 is much more than a technical toggle. In the March 27, 2026 context, the strongest model is to classify datastore types correctly, understand the difference between vSAN and general vSphere encryption patterns, design key-provider and TPM constraints carefully, and operate the whole control set in the language of ISO 27001 risk, evidence, and resilience.
Sources
- ISO - ISO/IEC 27001:2022 Information security management systems
- Broadcom Knowledge Base - Configure vSphere Native Key Provider
- Broadcom Knowledge Base - Windows VM fails to upgrade or deploy due to TPM not being enabled
- Broadcom Knowledge Base - Receiving general runtime error message. Native key provider is not compatible with host
- Broadcom Knowledge Base - Option "Use key provider only with TPM protected ESXi hosts" for non-homogenous cluster
- VMware/Broadcom - vSAN Technology Overview (2025 PDF)
- Wikimedia Commons - Inside Data Center