In the March 31, 2026 context, implementing VMware monitoring for ISO 27001 is not just about turning on a few alarms or forwarding logs to a syslog server. The short answer is this: the right model is to define which VMware signals matter, combine vCenter tasks-events-alarms with ESXi remote syslog and centralized log analysis, and then turn that flow into evidence that can stand up during audit review. This guide is written for teams that want a VMware monitoring model that is operationally useful and defensible under ISO 27001.
This guide is especially for:
- VMware and vSphere administrators
- security and compliance teams
- SOC, SIEM, and centralized logging teams
- IT leaders preparing for ISO 27001 audits
Quick Summary
- ISO 27001 does not ask for one specific VMware feature; it asks for a risk-based and reviewable monitoring model.
- VMware monitoring is not only dashboards. It includes tasks, events, alarms, syslog, and centralized correlation.
- vCenter tasks, events, and alarms are the first visibility layer.
- Without ESXi remote syslog, long-term and tamper-resistant log visibility is weaker.
- A central platform such as VMware Aria Operations for Logs or an enterprise SIEM should be part of the design.
- Wrong alarm targets and fragile syslog forwarding settings can create the illusion of monitoring without reliable evidence.
- The real ISO 27001 value comes from tying monitoring data to review, escalation, retention, and incident handling.
Table of Contents
- What Does VMware Monitoring Mean in ISO 27001 Terms?
- Which VMware Layers Must Be Monitored?
- How Should Alarming and Log Collection Be Designed?
- How Should the ISO 27001 Evidence Set Be Designed?
- What Mistakes Are Most Common?
- Practical Implementation Checklist
- Frequently Asked Questions
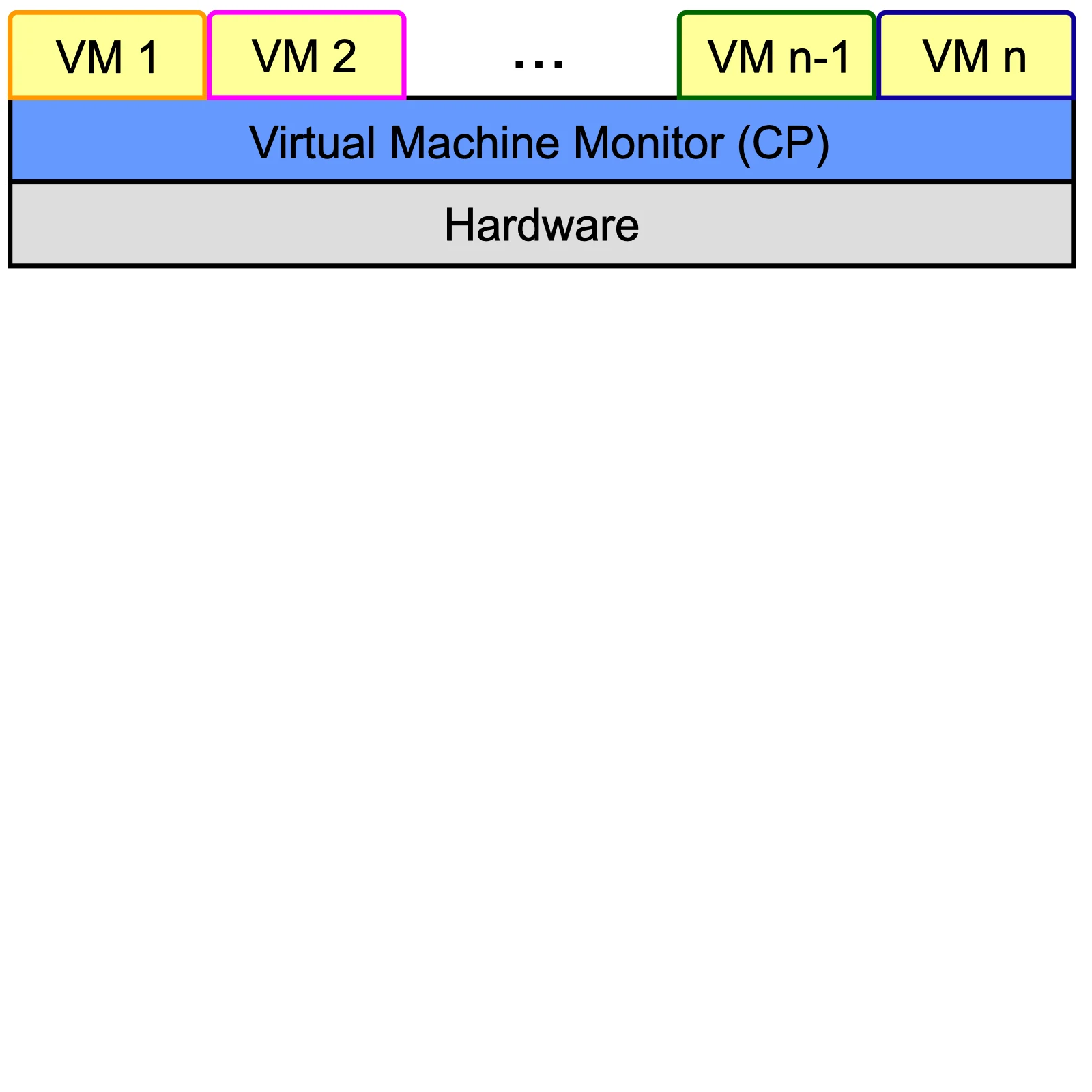
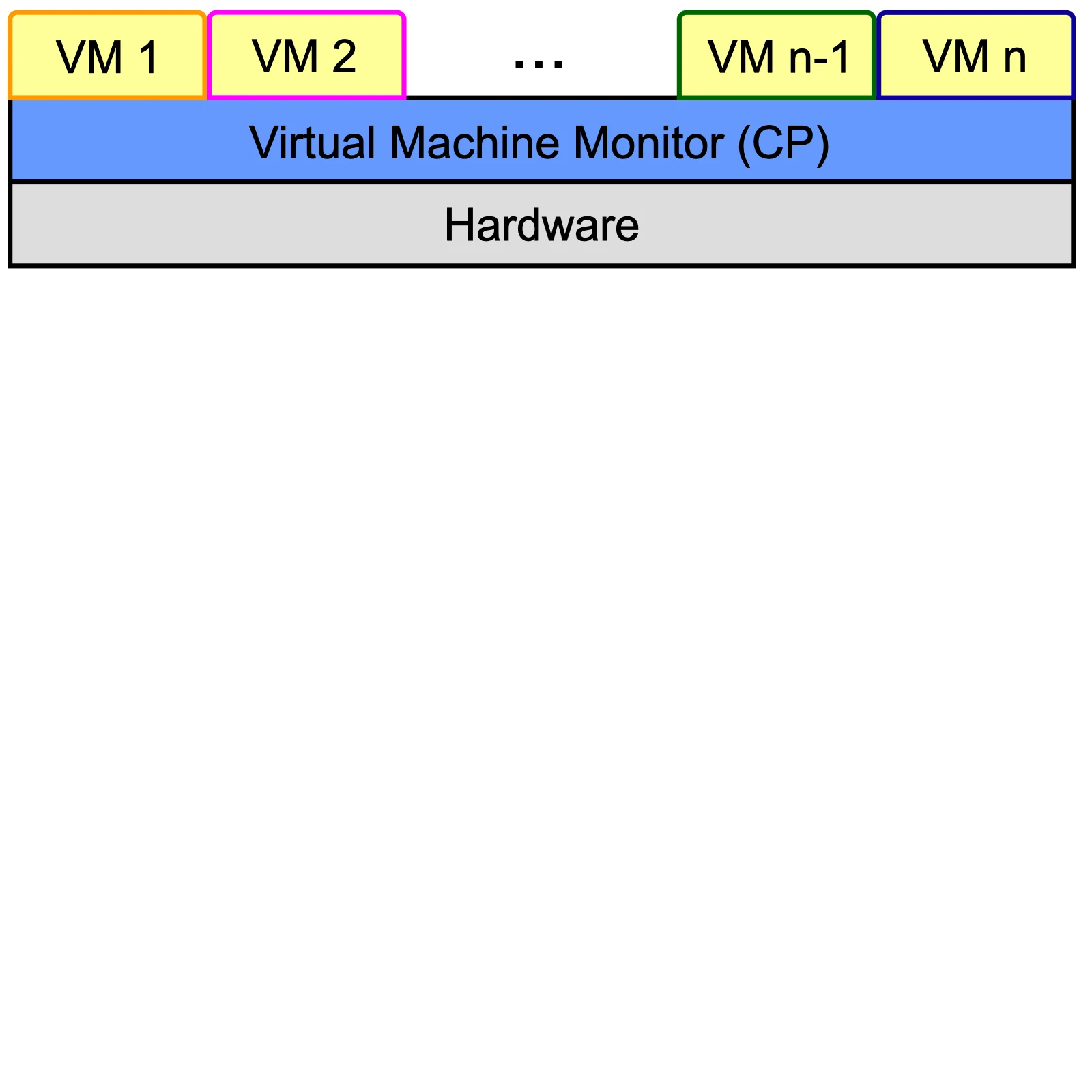
Image: Wikimedia Commons - VM Monitor.
What Does VMware Monitoring Mean in ISO 27001 Terms?
From the ISO 27001 perspective, the goal is not only to collect logs. The goal is to monitor relevant security and operational signals in a risk-based way, detect deviations, assign responsibility, and preserve evidence. ISO’s own information security guidance also frames the standard as a structured and strategic security approach, not just a technical checklist.
That means VMware monitoring should be designed around questions such as:
- which events are actually critical
- where alarms should exist
- which logs must reach a central platform
- how long data should be retained
- who reviews the signals and how often
- what records will be shown during audit
A stronger ISO 27001 monitoring model therefore means:
- not only producing alerts but defining the event lifecycle
- not only technical visibility but ownership and review cadence
- not only real-time notifications but a reliable audit trail
In short, VMware monitoring is not just a tool setup. It is a managed control.
Which VMware Layers Must Be Monitored?
1. vCenter tasks and events
VMware’s official vSphere documentation clearly shows that event retention, triggered alarms, recent tasks, and service or node health are core parts of the monitoring model. This layer is the first place to understand what is happening in the management plane.
In practice, the most relevant signals include:
- unexpected login activity
- host disconnect or reconnect events
- VM power operations
- snapshot, storage policy, or encryption changes
- patching, lifecycle, or scheduled-task behavior
- service health and node availability warnings
That is why Monitor > Tasks and Events in vCenter should be treated not only as a troubleshooting screen, but also as an evidence source.
2. vCenter alarms
Alarms are what turn visibility into operational action. Broadcom KB 377779 shows that custom alarms often fail because the wrong target type is selected. This matters because many teams believe they are monitoring a condition while the alarm is actually attached to the wrong object class.
A sound alarm model should clarify:
- whether the alarm belongs at the VM, host, or cluster level
- whether it is informational or action-driven
- whether it is for security use cases or operational use cases
- whether it remains only in the UI or also triggers mail, SIEM, or ticket actions
So in an ISO 27001 context, alarm design should not be judged by “how many alarms exist,” but by “are we monitoring the right object with the right trigger and escalation path?”
3. ESXi remote syslog
vCenter visibility alone is not enough. ESXi host logs must reach a central destination. Broadcom’s current KBs show that remote syslog forwarding can fail because of hostname or FQDN mismatches, and that non-standard syslog ports can behave differently depending on ESXi version and firewall behavior.
That means:
- a configured syslog target is not enough; the flow must be validated
- FQDN, hosts-file entries, and name resolution must be consistent
- if a non-standard port is used, the supported behavior must be verified
- scratch partition and logging health should be checked
From an ISO 27001 perspective, broken log forwarding is not only a technical issue. It weakens the control’s ability to generate evidence.
4. Centralized log analysis and correlation
Broadcom KB 324153 shows that vCenter integration with Aria Operations for Logs is part of the official vSphere monitoring story. Even if the organization uses a different SIEM, the principle remains the same: vCenter events, ESXi syslog, and related infrastructure logs should be correlated centrally.
This layer provides:
- environment-wide visibility instead of per-host troubleshooting only
- contextual review of alarms
- timeline reconstruction
- filtered, exportable evidence for audit windows
Related content:
- VMware Datastore Encryption for ISO 27001: Practical Guide
- How to Fix VMware Network Not Working
- How to Fix VMware vCenter Services Not Running
How Should Alarming and Log Collection Be Designed?
Build a layered model
The safest design is a layered one:
- vCenter visibility for tasks, events, and alarms
- ESXi remote syslog forwarding
- centralized searching and correlation
- notification or ticketing for critical alarms
- periodic review and retention governance
This makes the same signal useful for both operations and audit.
Document alarm purpose, trigger, and owner
At minimum, every important alarm should have:
- name and purpose
- target type
- threshold or event trigger
- severity
- action owner
- escalation path
- false-positive review cadence
Without this, alarms may exist, but the control is still immature.
Test the log flow continuously
The following should be part of regular validation:
- test event flow from ESXi to the log platform
- FQDN and name-resolution consistency
- real connectivity when non-standard ports are used
- time-to-visibility in the central platform
- whether critical alarms reach ticketing or notification channels
Broadcom KB 429006 and 418680 together show that “we configured it” is not the same as “it is reliably working.”
How Should the ISO 27001 Evidence Set Be Designed?
Audit evidence should be stronger than screenshots alone. A better VMware monitoring evidence set includes:
- scope list of monitored VMware components
- critical event matrix
- active alarm inventory and target definitions
- remote syslog configuration and validation proof
- sample central correlation outputs
- review meeting records or review logs
- links to incident or ticket records
- retention and export procedure
The strongest audit story usually includes:
- administrator login and privilege-change visibility
- host disconnect and HA-impacting events
- critical configuration change monitoring
- failed tasks, recurring error events, and persistent alarms
The underlying principle is simple: the monitoring system should show not only that an event occurred, but that it was noticed, reviewed, and handled.
What Mistakes Are Most Common?
Trusting only the vCenter UI
The vCenter UI is useful, but it is not enough without ESXi remote syslog and a central log platform.
Creating alarms with the wrong target
The alarm exists, but it is bound to the wrong object type, so nothing meaningful is detected.
Configuring syslog once and never validating it again
FQDN issues, port behavior, or silent forwarding failures can leave teams with a false sense of control.
Treating monitoring separately from incident handling
Under ISO 27001, seeing an alert is not enough. The response path matters too.
Failing to define retention and review
Logs are generated, but no one can explain how long they are kept, who reviews them, or how they are exported during audit.
Practical Implementation Checklist
- The monitored VMware components and critical event types were defined.
- vCenter tasks, events, and alarms were validated.
- Custom alarm target types were reviewed.
- ESXi remote syslog is active and tested.
- FQDN, port, and firewall behavior were validated.
- Central log correlation or SIEM ingestion was tested.
- Owners and escalation chains were assigned for critical alarms.
- Retention, review, and audit export procedures were documented.
Next Step with LeonX
Implementing VMware monitoring for ISO 27001 is not about showing a few dashboards. It is about operating vCenter visibility, ESXi log forwarding, and centralized event handling under one control model. LeonX helps organizations align VMware operations with audit evidence expectations in the same delivery flow.
Related pages:
- Hardware and Software Solutions
- SIEM and Security Incident Management Integration
- Cybersecurity Assessment Service
- Contact
Frequently Asked Questions
Is VMware monitoring for ISO 27001 just log collection?
No. Log collection is only one layer. The full model includes alarming, review, escalation, and evidence production.
Are vCenter alarms enough on their own?
No. Without ESXi remote syslog and centralized log analysis, the monitoring design remains incomplete.
Is a SIEM mandatory?
The specific platform can vary, but a central system capable of correlation, search, and evidence export is strongly needed. Aria Operations for Logs or an enterprise SIEM can serve that role.
If remote syslog is configured, is the problem solved?
No. Hostname, FQDN, port, and firewall issues can silently break forwarding, so validation tests are still required.
What evidence is strongest during audit?
Scope records, alarm definitions, syslog validation, central log outputs, review records, and incident-ticket links together create the strongest evidence set.
Conclusion
VMware monitoring for ISO 27001 is not about collecting more logs for the sake of it. It is about monitoring the right layers, turning events into meaningful alarms and correlation flows, and proving that the whole system is reviewed and managed. In the March 31, 2026 context, the strongest approach is to combine vCenter tasks-events-alarms, ESXi remote syslog, and centralized log management into an audit-ready operating model.
Sources
- ISO - ISO/IEC 27001:2022 Information security management systems
- ISO - Information security: A pillar of resilience in a digital age
- Broadcom Knowledge Base - vCenter integration with Aria Operations for Logs
- Broadcom Knowledge Base - ESXi host stops sending Syslog Data to remote syslog server due to hostname mismatch
- Broadcom Knowledge Base - ESXi hosts are unable to reach syslog non-standard port any port other than UDP/TCP 514 or TCP 1514
- Broadcom Knowledge Base - Non-default alarms are not getting triggered in vCenter
- Broadcom / VMware - VMware vSphere 6.7 PDF
- Wikimedia Commons - VM Monitor