VMware vCenter security is not just about stronger admin passwords or placing the interface behind a VPN. A stronger model secures the identity source, limits role and permission changes, manages certificate trust, makes session activity visible, and turns those controls into evidence that can stand up during an ISO 27001 audit. The short answer is this: for ISO 27001, vCenter security should be run as one control set across access, encryption, logging, and review.
This guide is especially useful for:
- VMware and vSphere administrators
- information security and compliance teams
- system teams responsible for Active Directory, SSO, and privileged access
- IT managers preparing for ISO 27001 audits
Quick Summary
- ISO/IEC 27001 uses a risk-based ISMS model, so vCenter security should be designed as a control framework rather than a checklist of product settings.
- Broadcom KB
316596explains how to secure the identity source by using LDAPS and validating the certificate/SAN relationship. - Broadcom KB
423205shows that vCenter 8.0 stores login activity in/var/log/audit/sso-events/audit_events.logwithLoginSuccess,LoginFailure, andLogoutevent types. - Broadcom KB
432327lists key audit-related events for SIEM forwarding, including authentication, permission, role, host-state, and VM reconfiguration events. - Broadcom KB
318946documents that Machine SSL and other vSphere certificates can be managed from the UI or withcertificate-manager, and that snapshots should be taken first. - Broadcom KB
376043shows how stale integration credentials can continuously triggerBadUsernameSessionEventand lock out AD accounts.
Table of Contents
- What Does vCenter Security Cover Under ISO 27001?
- How Should the Identity and Access Model Be Built?
- Why Are Certificates and Trust Critical?
- How Should Session and Audit Records Be Monitored?
- What Are the Most Common Mistakes?
- Related Content
- How Should the ISO 27001 Evidence Set Be Built?
- Checklist
- Next Step with LeonX
- Frequently Asked Questions
- Sources
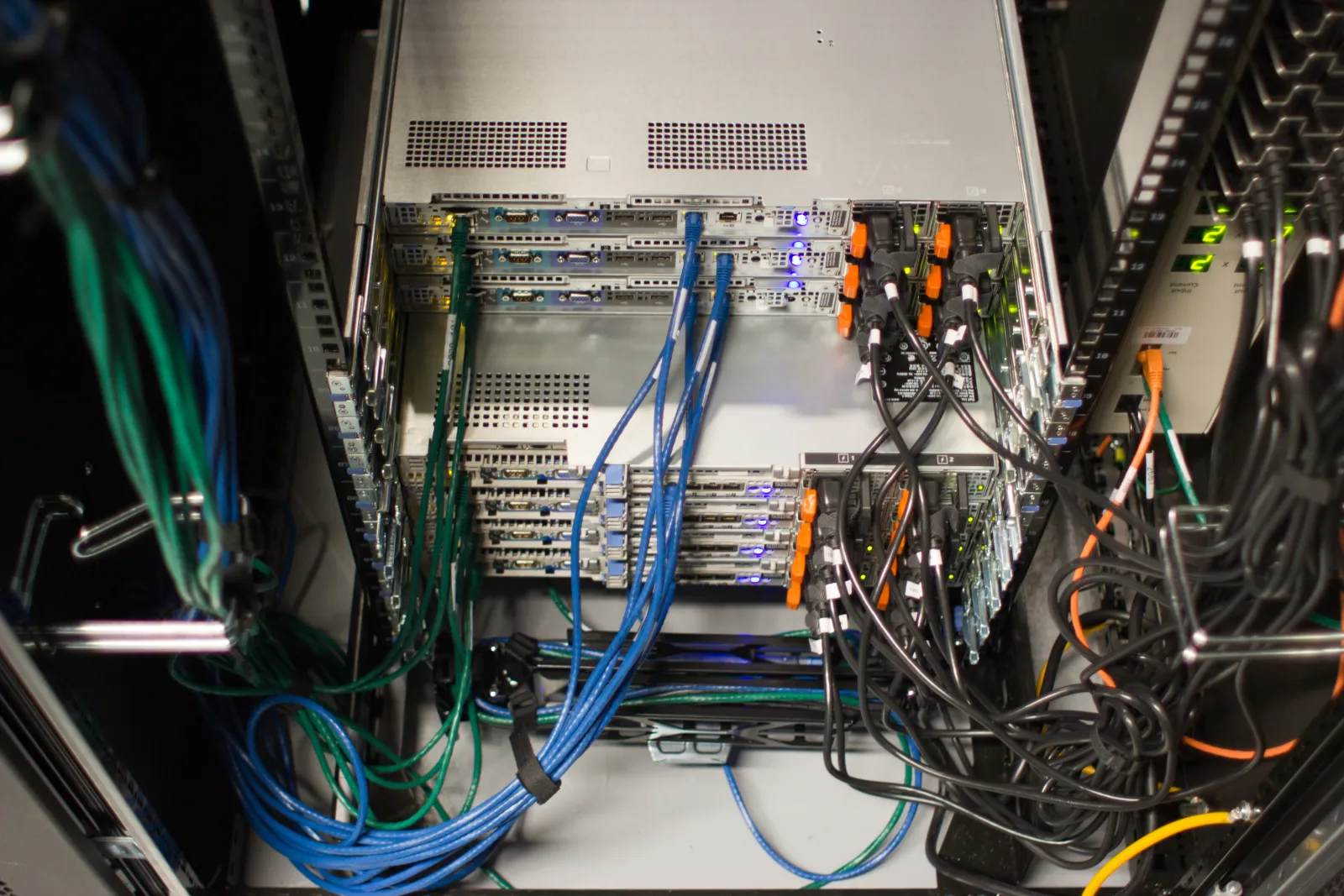
Image: Wikimedia Commons - Wikimedia Foundation Servers-8055 02.
What Does vCenter Security Cover Under ISO 27001?
The official ISO/IEC 27001 definition makes it clear that the standard is not about isolated product settings. It is about risk management, process control, and continual improvement. For vCenter, that means the core question is not “which checkbox is enabled?” but whether you can answer the following:
- who can access vCenter and through which identity source
- how privileged access is limited
- how certificate trust is governed
- how session and configuration records are reviewed
- how the whole model is evidenced during audit
In practice, ISO 27001-aligned vCenter security should cover:
- authentication and SSO
- role-based permissions and permission changes
- certificate lifecycle management
- successful, failed, and logout session records
- audit events forwarded to SIEM
- review, backup, and rollback discipline before sensitive changes
How Should the Identity and Access Model Be Built?
Why is LDAPS the first security layer?
Broadcom KB 316596 explicitly states that LDAP with SSL, meaning LDAPS, is the correct approach when you want to encrypt traffic between vCenter and the identity source. That matters for ISO 27001 because strong passwords are not enough if the identity path itself is not protected.
The KB also highlights three practical points:
- the Domain Controller certificate chain must be collected correctly
- the hostname used in the LDAP connection must appear in the DC certificate SAN
- an existing identity source for the same domain may need to be removed and re-added
So a defensible model is not just “AD integration exists,” but “identity integration is encrypted, certificate-validated, and documented.”
Why should role-based access be treated as its own control?
One of the most common vCenter security failures is giving a few broad admin accounts access to everything for convenience. However, KB 432327 shows that audit-related events include not only login activity, but also PermissionAddedEvent, PermissionUpdatedEvent, PermissionRemovedEvent, RoleAddedEvent, RoleUpdatedEvent, and RoleRemovedEvent.
That tells us:
- role design is a security control
- permission changes require centralized review
- creating, updating, and deleting custom roles all need audit visibility
A more defensible least-privilege model includes:
- limited roles for daily operations
- separate privileged accounts for maintenance
- separate identities for integrations and automation
- ticketed and reviewed workflow for critical permission changes
Why do failed login events matter operationally?
Broadcom KB 376043 shows that outdated integration credentials can generate repeated authentication failures and quickly lock out AD accounts. That means failed logins are not only attack indicators. They can also reveal weak credential lifecycle management.
For that reason, a stronger vCenter security model includes:
- a post-password-rotation checklist for every integration
- source IP review for repeated failed logins
- retirement of unused integration accounts
- separation between local and directory-based identities
Why Are Certificates and Trust Critical?
Broadcom KB 318946 shows that vSphere Certificate Manager can:
- implement default certificates
- replace the VMCA certificate with a custom CA certificate
- replace Machine SSL certificates
- manage certificates from the UI or the CLI
This matters in two ways:
1. vCenter security is not only password management
If the Machine SSL certificate is weak, expired, or badly governed, user trust, integration reliability, and external validation are all affected.
2. Certificate operations require controlled change management
KB 318946 explicitly recommends taking a snapshot before certificate work. In linked mode environments, the snapshot approach must be coordinated across linked vCenter instances. Under ISO 27001, that connects directly to change control and rollback readiness.
A healthier operational model includes:
- certificate inventory
- expiration calendar
- written standard for VMCA versus custom CA
- snapshot or backup plan before certificate changes
- post-change validation checklist
How Should Session and Audit Records Be Monitored?
Where are login records stored?
Broadcom KB 423205 states that vCenter Server 8.0 login records are stored in /var/log/audit/sso-events/audit_events.log, and that the file includes at least these event types:
com.vmware.sso.LoginSuccesscom.vmware.sso.LoginFailurecom.vmware.sso.Logout
That gives a strong starting point for ISO 27001 because it supports questions such as who logged in, from which client, whether the login failed, and whether the session was closed.
Which events should be forwarded to SIEM?
Broadcom KB 432327 groups the core vCenter audit events that should be considered for SIEM forwarding. The most relevant categories for vCenter security are:
- authentication and session events
- permission and role changes
- host connection and maintenance mode events
- VM creation, deletion, clone, and reconfiguration events
If those events never leave the local platform, audit visibility stays fragmented even if the vSphere UI still shows some history. That is why the security model should not stop at local review.
Why is centralized correlation necessary?
Login records, permission changes, and failed authentication activity should be correlated in a central log platform. This is where Business Management Services, especially the Cybersecurity Assessment Service, help evaluate control maturity. On the log pipeline side, Hardware & Software Services and SIEM and Security Event Management Integration help move vCenter audit activity into a centralized correlation model.
On the virtualization architecture side, Enterprise Virtualization Platforms Sales and Licensing supports the platform standard that sits underneath the control layer.
What Are the Most Common Mistakes?
Assuming AD integration is secure by default
An AD login that works is not automatically a secure identity model. LDAPS, certificate trust, and SAN validation still need to be checked.
Giving too much power to too many administrators
Reducing the number of roles is not the same thing as designing clean least-privilege roles. Fewer but more accurate roles are safer.
Reviewing login logs only after an incident
If LoginFailure or BadUsernameSessionEvent records are not reviewed regularly, both attack activity and broken integrations are found too late.
Leaving certificate renewal until the last moment
When Machine SSL and trust-chain work are delayed, access, integrations, and operations can all be put at risk at once.
Making permission changes outside ticketed process
Permission changes without ownership, approvals, and rollback thinking are much harder to defend during audit.
Related Content
- How to Monitor VMware for ISO 27001?
- VMware ESXi Hardening Guide for ISO 27001 Compliance
- What Is VMware vCenter and What Does It Do?
- How to Fix VMware vCenter Login Failed
How Should the ISO 27001 Evidence Set Be Built?
A strong audit evidence set for vCenter security is not just screenshots. It should include repeatable, time-bound records that show governance in operation. At minimum, it should include:
- identity source and LDAPS configuration standard
- privileged-access and role matrix
- permission and role change review records
- certificate inventory and renewal calendar
- example success and failure login records from
audit_events.log - list of vCenter event categories forwarded to SIEM
- integration password-rotation checklist
- snapshot, backup, and rollback procedure
Especially strong evidence includes:
- permission reviews from the last
12 months - incident or ticket records tied to repeated login failures
- pre-change and post-change certificate validation output
- approval trail for critical role or permission updates
Checklist
- the vCenter identity source was reviewed for LDAPS and certificate validation
- privileged and routine operational accounts were separated
- permission and role changes require review and ticket traceability
- Machine SSL and related certificate lifecycle dates were documented
- login success, failure, and logout records are reviewed regularly
- vCenter audit event categories for SIEM forwarding were defined
- integrations are validated after password rotation
- the vCenter security evidence set for audit is ready
Next Step with LeonX
VMware vCenter security is not a narrow hardening activity that ends after a few settings are changed. It is a governance model where identity, roles, certificates, logging, and review all operate together. LeonX helps you make that model more defensible through Business Management Services, especially the Cybersecurity Assessment Service, and complements it with SIEM and Security Event Management Integration plus platform-standard work across virtualization services. To review your current environment or request a proposal, continue through the Contact page.
Relevant pages:
- Business Management Services
- Cybersecurity Assessment Service
- SIEM and Security Event Management Integration
- Contact
Frequently Asked Questions
Is a strong admin password enough for vCenter security?
No. The identity source, permission model, certificate trust, and session logging all need to be governed together.
Why is LDAPS so important?
Because it encrypts the LDAP path between vCenter and the identity source and makes the trust relationship more defensible through certificate validation.
Where are vCenter login records stored?
According to Broadcom KB 423205, vCenter 8.0 login records are stored in /var/log/audit/sso-events/audit_events.log.
Are permission changes really part of audit scope?
Yes. Broadcom’s SIEM event guidance explicitly includes permission and role modification events in the audit-related set.
Should a snapshot be taken before certificate changes?
Yes. Broadcom KB 318946 explicitly recommends taking snapshots before certificate operations.
Conclusion
VMware vCenter security for ISO 27001 means securing the identity source, enforcing least privilege, managing certificate trust deliberately, centralizing login and change visibility, and turning all of that into defensible evidence. The strongest approach is to treat vCenter not only as a management console, but as a controlled and auditable layer in the enterprise security model.
Sources
- ISO/IEC 27001:2022 - Information security management systems
- Configuring a vCenter Single Sign-On Identity Source using LDAP with SSL (LDAPS)
- How to find vCenter Server login record
- Using vSphere Certificate Manager to Replace SSL Certificates
- Identifying Audit and security logs to forward to syslog server (SIEM)
- User AD account getting locked out and authentication failure errors are seen in vCenter events
- Wikimedia Commons - Wikimedia Foundation Servers-8055 02



